Recovering data from an encrypted drive demands both technical knowledge and reliable tools. When files vanish after encryption, simple undelete methods often fail, leaving users baffled. This guide explores the key strategies, tools, and precautions to restore deleted files from encrypted volumes while maintaining data integrity and security.
Understanding Disk Encryption and Its Impact on Deleted Files
Disk encryption uses complex algorithms to scramble data, making unauthorized access impossible without the correct key. Common solutions include BitLocker, VeraCrypt, FileVault, and LUKS. Encrypted volumes behave differently from standard partitions when files are deleted:
- Encrypted data blocks are cryptographically randomized, hindering straightforward recovery.
- Metadata structures—such as Master File Table (MFT) on NTFS or ext4 journaling—are also encrypted, masking file names and attributes.
- Standard recovery utilities may misinterpret encrypted sectors as empty space, overwriting critical remnants.
Understanding these factors is crucial for selecting the right approach. The process typically involves two major phases: decryption (or mounting the encrypted volume) and recovery (scanning and restoring files).
Preparatory Steps Before Initiating Recovery
Rushing into recovery without preparation often exacerbates data loss. Follow these essential steps:
1. Preserve the Encrypted Volume
Immediately stop using the affected drive to avoid overwriting recoverable data. Create a bit-level image (also called a forensic clone) of the encrypted partition using tools like dd or Guymager. This clone serves as a backup, allowing multiple recovery attempts without risk to the original.
2. Secure the Encryption Key or Password
Without the correct keyfile or passphrase, decryption is impossible. If you’ve lost the password, consider any password hints, keyfile backups, or external key escrow solutions you set up. Ensure you have:
- Backup of your keyfile or recovery key.
- Access to any key management system used by your organization.
3. Gather File System Information
Knowing the container type (LUKS, VeraCrypt, BitLocker), partition scheme (GPT, MBR), and file system (NTFS, ext4, APFS) helps tailor the recovery method. Use tools like fdisk, parted, or Disk Management (Windows) to inspect partition layouts.
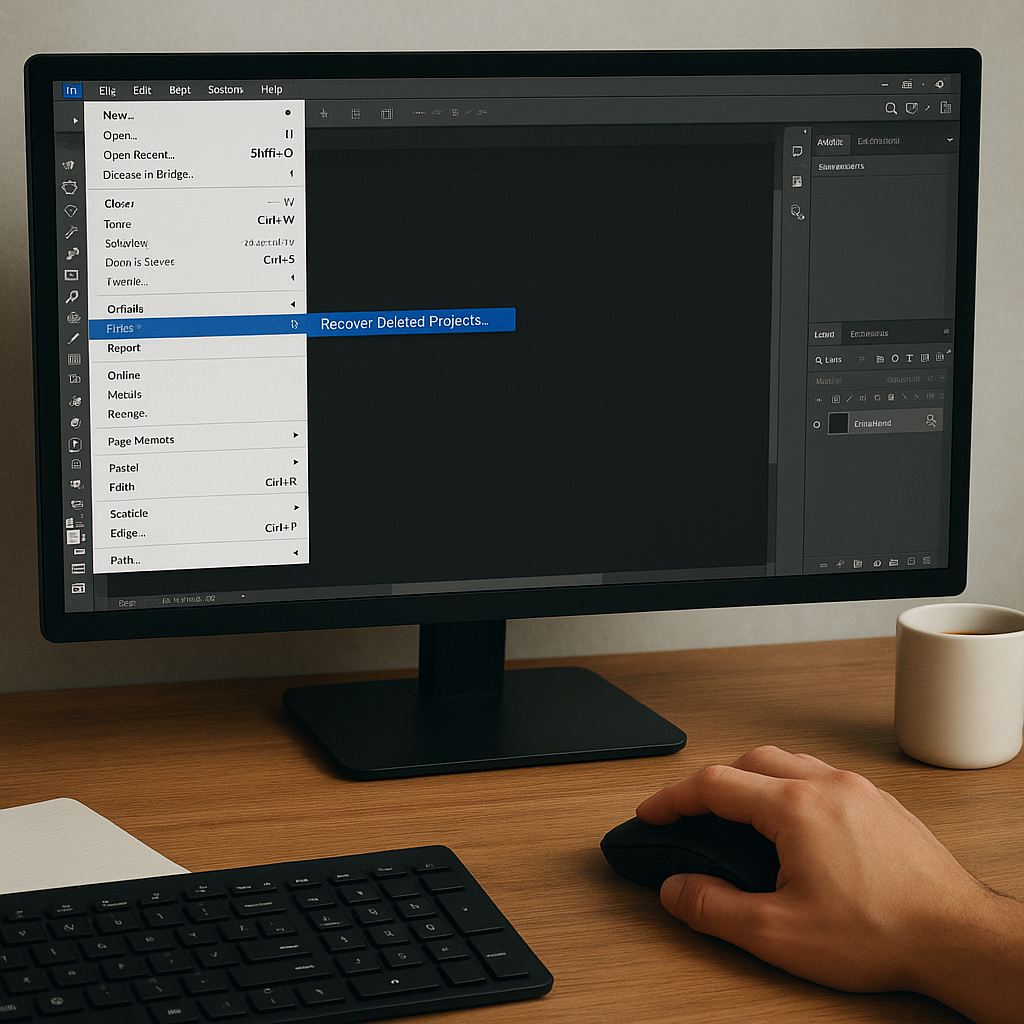
Using Recovery Software on Decrypted Images
After successfully mounting or decrypting the volume, apply specialized recovery software to identify and extract deleted files. Popular tools include:
- R-Studio – Offers robust scanning for various file systems.
- Recuva – User-friendly interface ideal for basic NTFS recovery.
- PhotoRec – Signature-based recovery, effective for media and documents.
- TestDisk – Recovers lost partitions and rebuilds file system structures.
- EaseUS Data Recovery Wizard – Simplifies the process with guided steps.
Step-by-Step Recovery Workflow
- Install and launch your chosen recovery software on a separate system or drive.
- Select the mounted decrypted volume or its image as the target.
- Choose a deep scan or full recovery mode to detect hidden and deleted files.
- Filter results by file type, size, or deletion date to narrow down candidates.
- Preview recoverable files to verify integrity before saving.
- Restore files to a different physical drive to avoid overwriting.
During this process, maintain a detailed log of recovered items, software settings, and any anomalies. This documentation aids further attempts if initial scans miss critical data.
Advanced Techniques for Encrypted Volumes
When standard recovery tools struggle, consider these advanced tactics:
Encrypted Metadata Extraction
In certain cases, metadata remnants exist outside the main data area. Tools such as EnCase or X-Ways Forensics can carve encrypted headers and decrypted structures from memory dumps or hibernation files, revealing clues on file locations.
Using a Virtual Machine Sandbox
Mount the encrypted drive image within a virtual machine equipped with the exact disk encryption software version. This minimizes driver mismatches and permits low-level access to volume structures. It also isolates the process, preserving your host system’s stability.
Hex-Level Manual Recovery
If automated scans fail, a manual approach may help. Open the drive image in a hex editor (HxD, WinHex). Search for known file signatures (e.g., JPEG starts with FF D8 FF). Once detected:
- Mark start and end offsets.
- Extract the sector range as a new file.
- Rename with the correct extension and test file validity.
This labor-intensive process can rescue critical files that elude GUI tools. Success hinges on understanding file structure and encryption padding schemes.
Best Practices to Prevent Future Data Loss
Implementing proactive measures reduces the risk of permanent data loss:
- Consistent Backups – Schedule automated full and incremental backups. Store copies in separate physical locations or cloud services.
- Regular Key Escrow – Maintain up-to-date recovery keys in a secure vault, ensuring you can always decrypt critical volumes.
- Versioned File Systems – Use snapshot-capable file systems (ZFS, Btrfs) or volume shadow copies (Windows) to retain historical versions.
- Audit Trails – Keep logs of encryption and decryption operations, user access, and system changes.
- Routine Health Checks – Monitor disk SMART attributes and run file system integrity tools periodically.
By combining these precautions with reliable recovery software, you dramatically increase your chances of restoring files after accidental deletion or corruption on encrypted drives. The key lies in disciplined preparation, informed tool selection, and careful execution throughout the recovery process.