Recovering files from an inaccessible partition can feel like navigating a labyrinth where every turn leads to uncertainty. A well-chosen recovery tool not only simplifies the process but also minimizes the risk of permanent data loss. This guide explores the fundamentals, key software capabilities, a step-by-step retrieval workflow, and best practices to safeguard your precious information.
Understanding Partition Inaccessibility
Partitions may become inaccessible for various reasons, ranging from logical errors to hardware failures. When a partition fails to mount or returns error messages such as “drive not formatted” or “access denied,” the underlying file system might be corrupted. Common triggers include abrupt power outages, improper shutdowns, virus attacks, or faulty disk controllers. Before diving into recovery, it is crucial to grasp the causes:
- Logical corruption due to unexpected system crashes
- Accidental formatting or deletion of partition tables
- Bad sectors caused by physical damage over time
- Malware or ransomware locking the partition
- Windows, macOS, or Linux upgrade failures
Identifying the root cause informs your approach: a superficial error might yield to a quick scan, whereas deeper issues require advanced imaging or specialized recovery engines.
Essential Recovery Software Features
Not all recovery applications are created equal. Selecting a tool with a robust feature set ensures higher success rates and fewer headaches. Look for these must-have capabilities:
- Deep scan algorithms that examine disk sectors byte by byte
- Partition table reconstruction to restore lost volume metadata
- Support for multiple file systems (NTFS, FAT, exFAT, HFS+, ext4, etc.)
- Raw recovery mode for file signature-based retrieval
- Preview functionality to confirm recoverable files before extraction
- Disk imaging to create sector-by-sector clones without altering the original
- User-friendly interface with guided wizards for novices and expert modes for professionals
- High performance and multithreaded scanning to reduce wait times
- Integrity checks that validate recovered files against checksums
- Secure wiping options for drives you intend to repurpose
A reliable solution should strike a balance between technical depth and intuitive design, enabling both casual users and IT specialists to navigate complex scenarios.
Step-by-Step Recovery Process
Preparing the Environment
Before launching any recovery operation, ensure you have the right setup:
- Download and install the recovery software on a different physical drive than the affected partition
- Gather an external USB or network location with enough free space to store recovered files
- Disable any system maintenance tasks or antivirus scans that could interfere with the process
- Note the partition’s original specifications: size, file system type, and label
This precautionary stage mitigates accidental overwrites and keeps the damaged partition untouched.
Performing the Initial Scan
Most tools offer a choice between a quick scan and a full deep scan:
- Quick scan: Rapidly locates recently deleted files by reading the Master File Table or equivalent metadata. Ideal if you accidentally deleted the partition or formatted it.
- Deep scan: Conducts an exhaustive search across all sectors, reconstructing lost structures. Recommended for severe corruption or if the quick scan yields insufficient results.
Initiate the selected scan, then monitor progress. Depending on drive size, the process could take from minutes to several hours. During scanning, the software identifies recoverable items and categorizes them by file type.
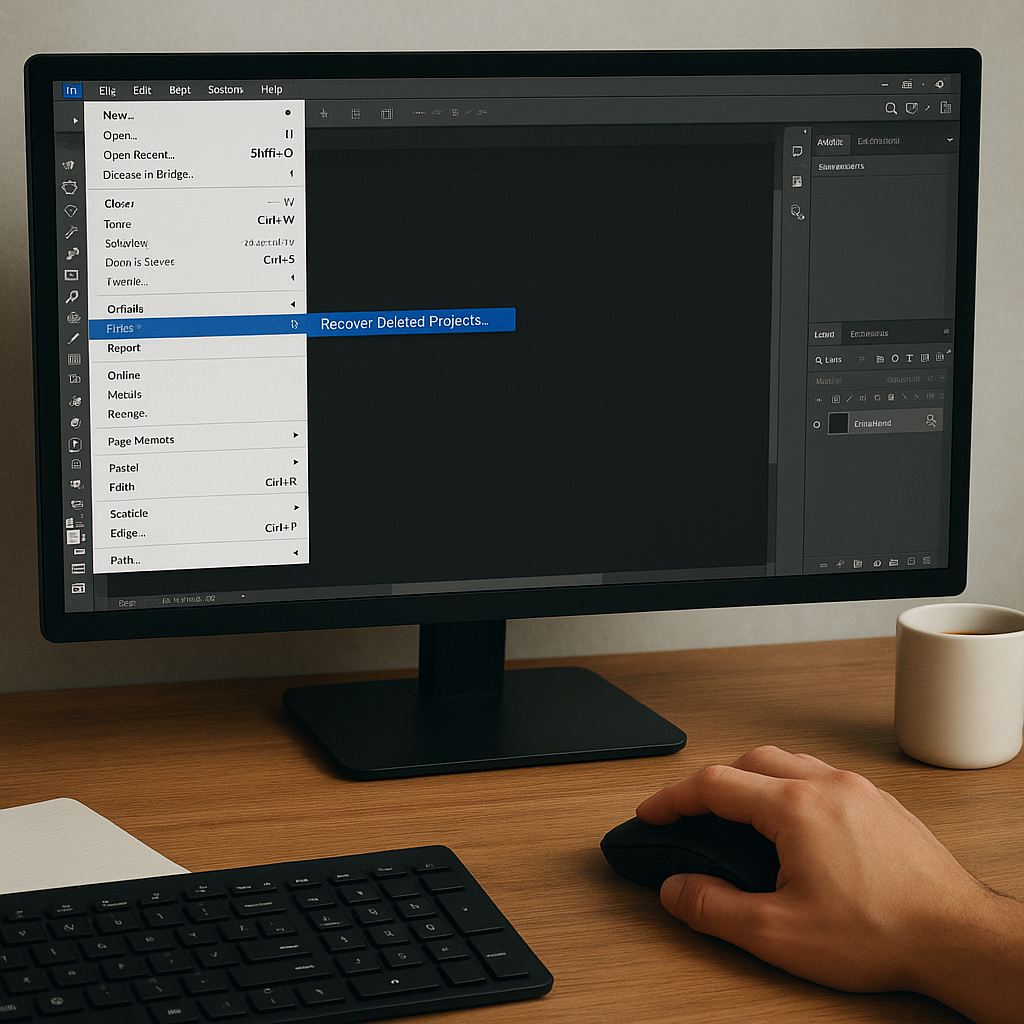
Selecting and Restoring Files
Once scanning completes, the recovery tool presents a tree of folders or a list of discovered files. Follow these steps for efficient restoration:
- Use filters to narrow results by file extension, size, or modification date.
- Preview critical documents, photos, and videos to verify their integrity.
- Choose a secure destination—never the original partition—to avoid overwriting lost data.
- Initiate the recovery and keep an eye on notifications for read errors or sector failures.
After extraction, open a handful of files to ensure they are intact. If certain items appear garbled or incomplete, revisit the scan results and attempt a different recovery mode.
Preventive Measures and Best Practices
Once your data is safe, shift focus to preventing future loss. Establish a routine that includes:
- Regular backup schedules leveraging both local and cloud solutions
- Disk health monitoring using S.M.A.R.T. tools or third-party utilities
- Avoiding frequent partition resizing without proper expertise
- Implementing a reliable UPS to protect against power surges and sudden outages
- Using antivirus solutions and practicing safe browsing habits
These practices minimize the odds of encountering inaccessible partitions and reduce recovery complexity when issues arise.
Advanced Topics and Troubleshooting
In some scenarios, you might face unique challenges that demand advanced techniques:
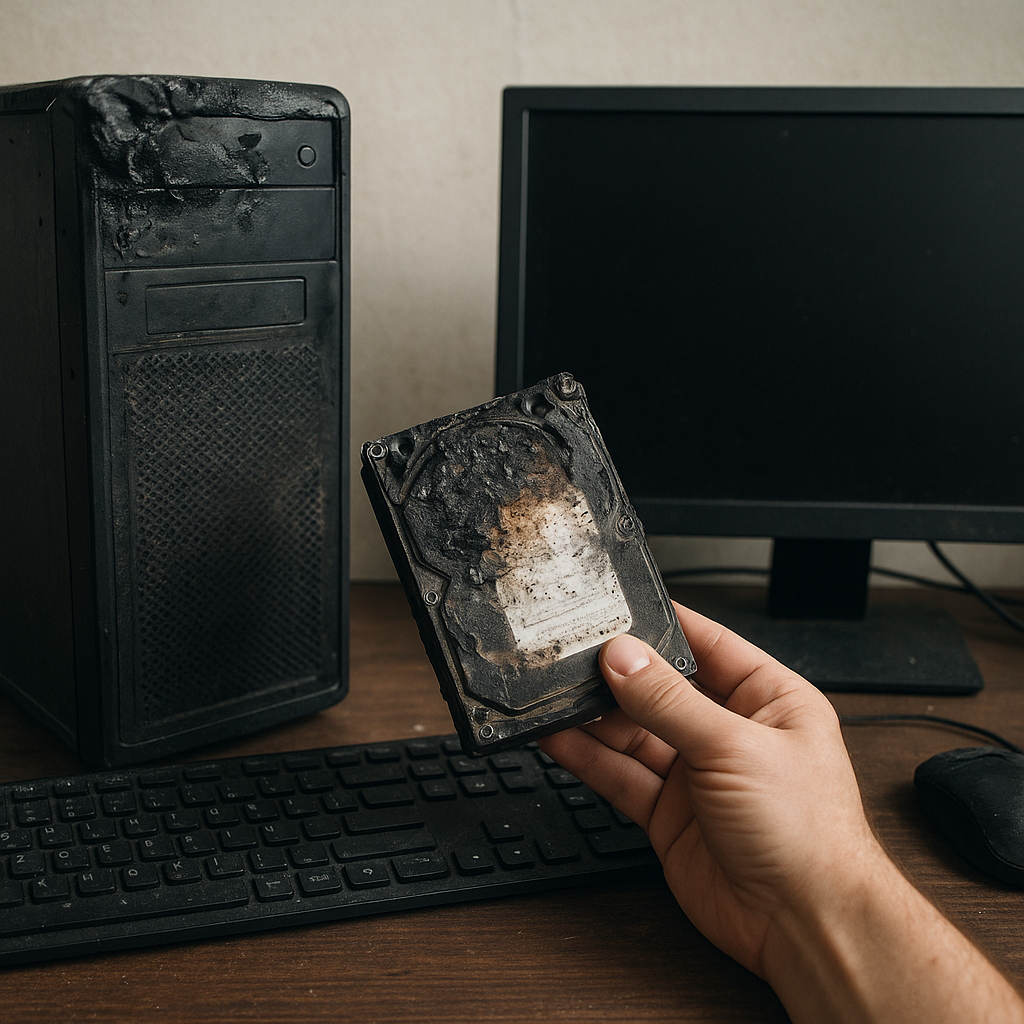
Imaging Faulty Drives
When bad sectors proliferate, perform a sector-by-sector copy to an image file. Use tools that skip unreadable blocks while retaining recoverable data. Work on the image, not the live drive.
Handling Encrypted Partitions
Encrypted volumes require the original key or passphrase. If you lack credentials, recovery becomes nearly impossible. Always store encryption keys in secure, redundant locations.
Dealing with Unsupported File Systems
Some recovery programs may not support niche or proprietary file systems. In such cases, seek specialized utilities or consult professional data recovery services.
Log Analysis and Support Channels
Most recovery applications generate detailed logs. When errors occur, review these entries for clues. Developers’ forums and vendor support can guide you through obscure error codes and recovery tweaks.
Mastering file retrieval from inaccessible partitions demands patience, the right tools, and disciplined procedures. By embracing sound recovery principles, you can reclaim lost information and fortify your systems against future mishaps.